I have recently installed and configured my 2 node F5 BIG-IP cluster as load-balancer and SSL-VPN portal. I have been ocasionally performing configuration backups, but now i need to schedule them regularly and automatically.
This article covers the ways to perform the backup of a BIG-IP system and automate them.
Manual backup
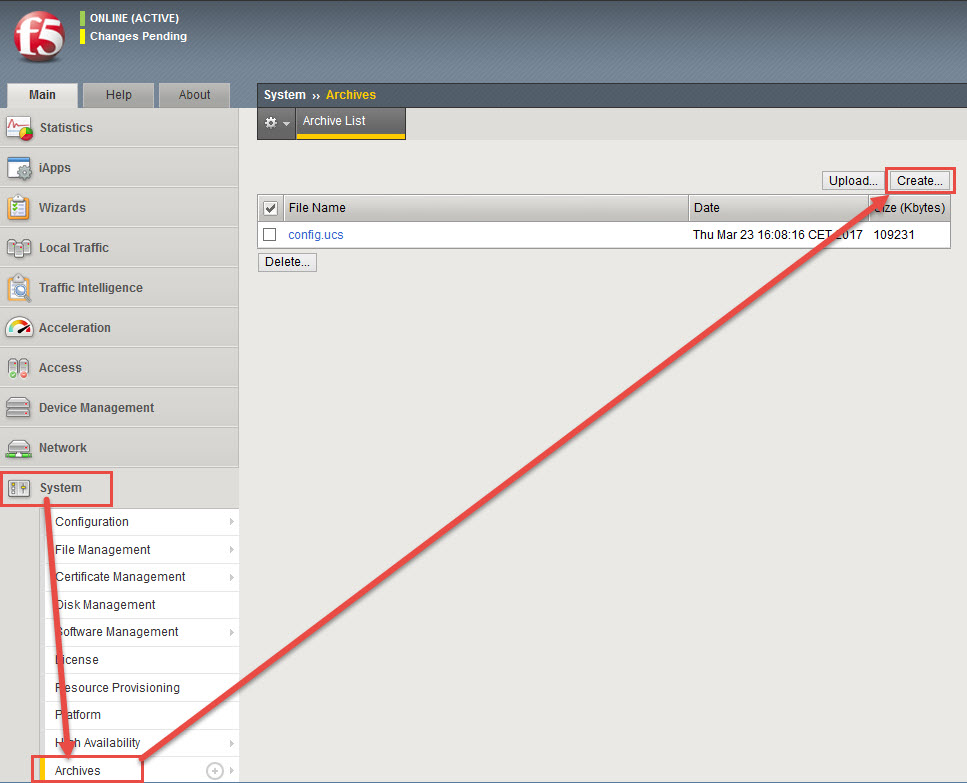
Web GUI
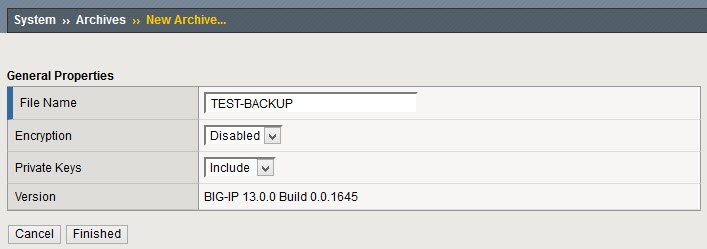
In the menu options: System – Archives – Create
The newly created backup should appear
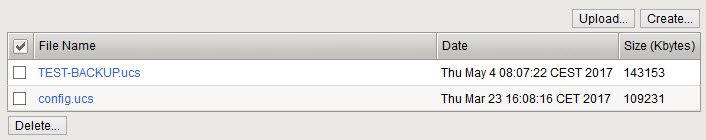
By doing this way, these .ucs files are stored by default in /var/local/ucs folder:
[root@BigIP1:Active:In Sync] config # ls -l /var/local/ucs/*.ucs
-rw-r--r--. 1 root root 111852971 2017-03-23 16:08 /var/local/ucs/config.ucs
-rw-r--r--. 1 root root 146589180 2017-05-04 08:07 /var/local/ucs/TEST-BACKUP.ucsCommand
After SSH logging, open the tmsh cli and use the save command
save /sys ucs <path to save ucs file>For example
root@(BigIP1)(cfg-sync In Sync)(Active)(/Common)(tmos)# save /sys ucs /var/tmp/TEST-BACKUP2.ucs
Saving active configuration...
08:11:24 Running cs_save_pre_script on Thu May 4 08:11:24 CEST 2017
08:11:25 F5_INSTALL_SESSION_TYPE=, is_provisioned avr=0, is_provisioned dos=0, is_provisioned pem=0, is_provisioned afm=0, is_provisioned swg=0, is_provisioned asm=0, Avr.Upgrade.Enabled=true
08:11:25 Not Running AVR backup procedure.
08:11:25 Finished cs_save_pre_script.
08:11:25 /var/tmp/TEST-BACKUP2.ucs is saved.
root@(BigIP1)(cfg-sync In Sync)(Active)(/Common)(tmos)# quit
[root@BigIP1:Active:In Sync] config # ls -l /var/tmp/*.ucs
-rw-r--r--. 1 root root 146590659 2017-05-04 08:11 /var/tmp/TEST-BACKUP2.ucs
[root@BigIP1:Active:In Sync] config #Given that this example backup was not stored in the default ucs location (/var/local/ucs), this one will not appear in the Web GUI – Archives section.
Automated backup
Configure SSH access with key public-private key authentication
If haven’t done before, the key pair must be generated in the client machine:
server01:~# ssh-keygen -t rsa
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa.
Your public key has been saved in /root/.ssh/id_rsa.pub.
The key fingerprint is:
df:79:c7:44:7c:0a:7f:a2:77:b1:1d:6a:41:2f:f1:43 root@server01
Copy the public key into the BIGIP authorized_keys file (this should the last time you are prompted for password):
server01:~# ssh bigip1 'cat .ssh/id_rsa.pub' >> ~/.ssh/authorized_keys
Password:Now SSH connection without password prompt!:
server01:~# ssh bigip1
Last login: Tue May 2 13:32:53 2017 from 10.0.50.30
[root@BigIP1:Active:Changes Pending] config #
Script to generate and copy UCS file (backup)
Using the previosly shown tmsh command (save /sys ucs), this script can be executed in a machine to remotely generate and copy a configuration backup to a desired path:
#!/bin/sh
TIMESTAMP=`date +%Y%m%d`
REMOTE_PATH="/var/tmp"
LOCAL_PATH="/MYBACKUPS/BACKUPS_BIGIP"
REMOTE_BIGIP=bigip1
BACKUP_FILENAME=${REMOTE_BIGIP}_$TIMESTAMP.ucs
ssh $REMOTE_BIGIP tmsh save /sys ucs $REMOTE_PATH/$BACKUP_FILENAME > /dev/null
scp $REMOTE_BIGIP:$REMOTE_PATH/$BACKUP_FILENAME $LOCAL_PATH/
ssh $REMOTE_BIGIP rm $REMOTE_PATH/$BACKUP_FILENAME
The script:
– Executes remotely the tmsh command to generate the .ucs file
– Copies the remote .ucs file to the configured local path
– Removes the remote copy of the file
Crontab to schedule the backup script
After testing the script works correctly, it can be scheduled using cron:
# m h dom mon dow command
30 7 * * 1 /MyScripts/BACKUP_F5_BIGIP.sh
MAILTO=""This example backup is scheduled every monday at 7:30 am
(extra) Email backup notification
If your Linux system is configured to send emails (using mail command), you can add the following lines at the end of the script to send notifications containing an “OK” of “Fail” result of the backup process:
MSG_BODY="This notification has been generated by the script script... located in ... "
if [ -f $LOCAL_PATH/$BACKUP_FILENAME ]
then
MSG_SUBJECT="Backup $REMOTE_BIGIP OK ($BACKUP_FILENAME)"
else
MSG_SUBJECT="Backup $REMOTE_BIGIP FAIL!!"
fi
echo "$MSG_BODY" | mail -aFrom:Sender\<sender@domain.com\> recipient@domain.com -s "$MSG_SUBJECT"
