NAT (Network Address Translation) can be configured in our Checkpoint FW in 2 two different ways: Manual or Automatic
Automatic NAT
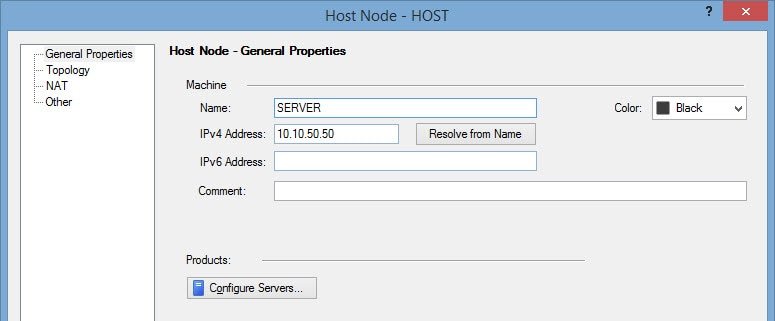
To configure the automatic NAT, the SERVER object properties has a NAT section.
So for example, if we want our host with internal private IP 10.10.50.50 to be published in Internet with public IP 80.80.100.100:
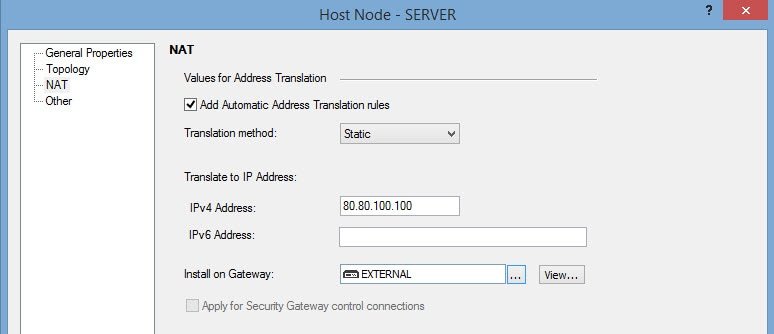
(I we only wanted to apply outbound IP masquerading, we should have applied hide NAT type.
In this example, we are also trying to publish to Internet to receive incoming connections, so static NAT type.)
For more details, visit my post Checkpoint – Hide NAT vs Static NAT
This NAT configuration automatically performs 2 actions:
1. Creation of the corresponding NAT rule
| Original Packet | Translated Packet | ||||
| Source | Destination | Service | Source | Destination | Service |
| Any | 80.80.100.100 | Any | Original | 10.10.50.50 | Original |
2. Configuration of the corresponding Proxy ARP
After applying the automatic NAT configuration, the firewall will start reply to the ARP request asking for the 80.80.100.100 public IP. Then the firewall will 'NAT' the packet and route it to the proper gateway or to the final destination.
Its very important to apply the NAT section of the host only to the gateway we want (Instead of all, the default option)

Otherwise, in a VSX environment, all VS firewalls can start to reply those ARP request, and so, steal packets among them.
Manual NAT
To configure manual NAT, instead of using the NAT section of our HOST object we can add rules on the NAT section of our firewall policy.
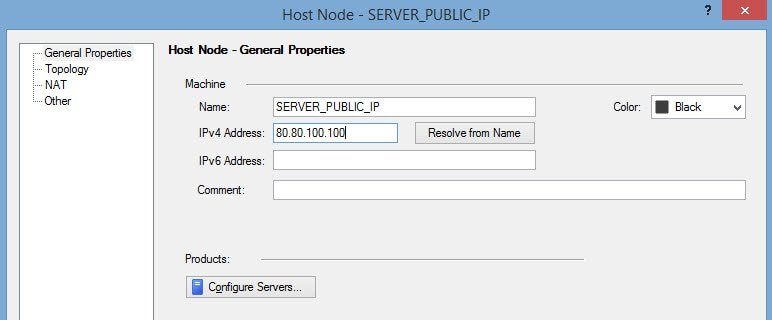
To recreate the same NAT configuration as the previous example, there must also be another HOST object with the public IP configured
And then we can create the NAT rule:

As I said, the automatic NAT method configures the proxy ARP automatically.
When using manual NAT, the proxy ARP must be added manually. Check this post "Checkpoint – Proxy ARP for manual NAT on VSX" for more information
Manual NAT vs Automatic NAT
Then, if manual NAT requires more configurations, why should I use it?? Good question.
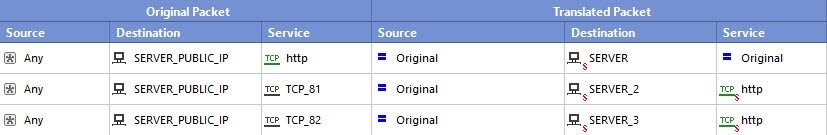
Sometimes we need to perform NAT based on destination port (or any combination based on the source IP, destination IP, port…)
For example:
When accesing the public IP, the destination internal IP the firewall NATs to depends on the destination port:
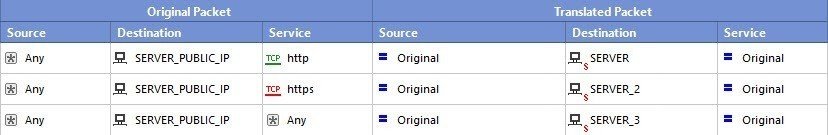
Or this rule allows us to access three different internal servers on the same port with a single public IP (based on the original packet destination port)
So, if the NAT rule is simple, better use Automatic NAT. Otherwise, your only option is using the Manual NAT method.